Elliptic Curve Accelerator for zkSNARKs
From iis-projects
Short Description
A Zero Knowledge Proof allows one entity (the prover) to prove a statement to another party (the verifier) without revealing the secrets required to proof the statement. For example Alice can prove to Bob that she knows the solution to a problem (e.g sudoku) without revealing the solution itself. It is believed that such systems will enable a lot of new systems and protocols. One such example is ZCash. ZCash is a cryptocurrency that uses Zero Knowledge Proofs (zkSNARKs) to keep the users privacy protected. A shielded ZCash transaction does neither reveal the amount transfered nor the participating parties. The resulting transaction is completely private but it still guarantees the correctness of the transaction: the input and output values add to zero and the sender actually owns the coins that he spends. ZCash would enable a distributed electronic cash systems with no compromises in user privacy.
There is a catch however: creating a zkSNARK requires a lot of computational power and energy and software implementations take 10s of seconds on a current processors. A lot of recent research tries to improve the performance of these Zero Knowledge Proofs in software but without significant improvements, it is impossible to create a proof on a mobile phone.
Technical Description
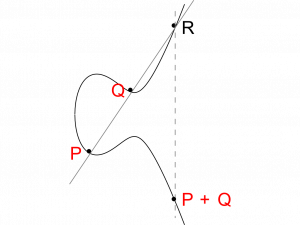
Creating a zkSNARK involves more than 10'000 elliptic curve operations on a specific pairing friendly curve and these operations are expensive and slow. Custom hardware accelerators could enable a much faster and energy efficient proof generation. In this project you would investigate the feasibility of an elliptic curve accelerator for the specific curves used in ZCash. You will devise an optimal architecture for the problem and implement it on an FPGA.
Status: Available
- Looking for 1-2 Semester/Master students
- Contact: Moritz Schneider
Prerequisites
- VLSI I
- VLSI II (recommended)
- Experience with elliptic curve cryptography and their implementations
Character
- 40% Theory
- 40% Digital Design
- 20% Verification