Difference between revisions of "ASIC Implementation of Jammer Mitigation"
From iis-projects
(Created page with "400px|thumb|A jammer tries to disrupt multiple user equipments from transmitting data to a basestation by injecting interference. ==Short D...") |
|||
| (6 intermediate revisions by the same user not shown) | |||
| Line 1: | Line 1: | ||
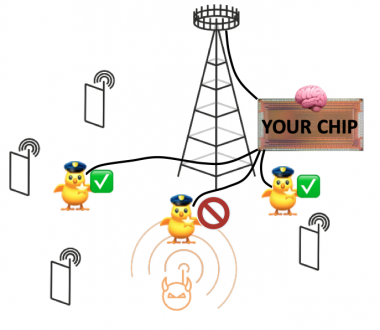
| − | [[File:jammer_mitigation_asic.png| | + | [[File:jammer_mitigation_asic.png|380px|thumb|A MIMO basestation mitigates an ongoing jamming attack while continuing to serve the legitimate user equipments. The signal processing for this takes place in a custom ASIC.]] |
==Short Description== | ==Short Description== | ||
| − | + | Jamming attacks pose a critical threat to wireless communication systems. Multi-antenna (MIMO) wireless systems have the potential to mitigate such jamming attacks through signal processing. Methods for jammer mitigation are thus currently a hot research topic in wireless communication. Many different linear [1], [2] and non-linear (e.g., deep learning based [3]) jammer mitigation algorithms have been proposed. To be practically viable, such methods will ultimately have to be implemented in hardware (using FPGAs or, more likely, ASICs), since sofware-based signal processing will never support the data rates of modern wireless systems. To this date, however, there are no hardware implementations of jammer mitigation algorithms. | |
| − | + | The goal of this project is to develop the first ASIC implementation of a jammer-mitigating signal processing algorithm. For this, the student will take a state-of-the art jammer mitigation algorithm and adapt it as an efficient VLSI implementation. The student will then synthesize this design and tape out a chip using CMOS technology. | |
| + | |||
| + | |||
| + | [1] Q. Yan, H. Zeng, T. Jiang, M. Li, W. Lou, and Y. T. Hou "Jamming resilient communication using MIMO interference cancellation." IEEE Transactions on Information Forensics and Security 11(7), 2016, 1486-1499. | ||
| + | |||
| + | [2] H. Akhlaghpasand, E. Björnson, and S. Mohammad Razavizadeh. "Jamming suppression in massive MIMO systems." IEEE Transactions on Circuits and Systems II: Express Briefs 67(1), 2019, 182-186. | ||
| + | |||
| + | [3] T. Erpek, Y. E. Sagduyu, and Y. Shi. "Deep learning for launching and mitigating wireless jamming attacks." IEEE Transactions on Cognitive Communications and Networking 5(1), 2018, 2-14. | ||
| − | |||
===Status: Available === | ===Status: Available === | ||
| − | : Looking for | + | : Looking for 1-2 Semester/Master students |
: Contact: [https://iip.ethz.ch/people/profiles.MTk4MzMz.TGlzdC80MTExLDEwNjY3Mjg3NDU=.html Gian Marti] | : Contact: [https://iip.ethz.ch/people/profiles.MTk4MzMz.TGlzdC80MTExLDEwNjY3Mjg3NDU=.html Gian Marti] | ||
| Line 53: | Line 59: | ||
==Links== | ==Links== | ||
| − | [[Category: | + | [[Category:Completed]] |
[[Category:IIP]] | [[Category:IIP]] | ||
[[Category:IIP_5G]] | [[Category:IIP_5G]] | ||
| + | [[Category:2022]] | ||
[[#top|↑ top]] | [[#top|↑ top]] | ||
Latest revision as of 13:31, 10 May 2023
Contents
Short Description
Jamming attacks pose a critical threat to wireless communication systems. Multi-antenna (MIMO) wireless systems have the potential to mitigate such jamming attacks through signal processing. Methods for jammer mitigation are thus currently a hot research topic in wireless communication. Many different linear [1], [2] and non-linear (e.g., deep learning based [3]) jammer mitigation algorithms have been proposed. To be practically viable, such methods will ultimately have to be implemented in hardware (using FPGAs or, more likely, ASICs), since sofware-based signal processing will never support the data rates of modern wireless systems. To this date, however, there are no hardware implementations of jammer mitigation algorithms.
The goal of this project is to develop the first ASIC implementation of a jammer-mitigating signal processing algorithm. For this, the student will take a state-of-the art jammer mitigation algorithm and adapt it as an efficient VLSI implementation. The student will then synthesize this design and tape out a chip using CMOS technology.
[1] Q. Yan, H. Zeng, T. Jiang, M. Li, W. Lou, and Y. T. Hou "Jamming resilient communication using MIMO interference cancellation." IEEE Transactions on Information Forensics and Security 11(7), 2016, 1486-1499.
[2] H. Akhlaghpasand, E. Björnson, and S. Mohammad Razavizadeh. "Jamming suppression in massive MIMO systems." IEEE Transactions on Circuits and Systems II: Express Briefs 67(1), 2019, 182-186.
[3] T. Erpek, Y. E. Sagduyu, and Y. Shi. "Deep learning for launching and mitigating wireless jamming attacks." IEEE Transactions on Cognitive Communications and Networking 5(1), 2018, 2-14.
Status: Available
- Looking for 1-2 Semester/Master students
- Contact: Gian Marti
Prerequisites
- Verilog or VHDL
- VLSI II
- Familiarity with the basics of digital communication is recommended but not strictly required
Character
- 80% VLSI Implementation and Verification
- 20% MATLAB simulation