Difference between revisions of "A Unified-Multiplier Based Hardware Architecture for Elliptic Curve Cryptography"
From iis-projects
(Created) |
m (→Update categories) |
||
| (3 intermediate revisions by the same user not shown) | |||
| Line 1: | Line 1: | ||
| + | __NOTOC__ | ||
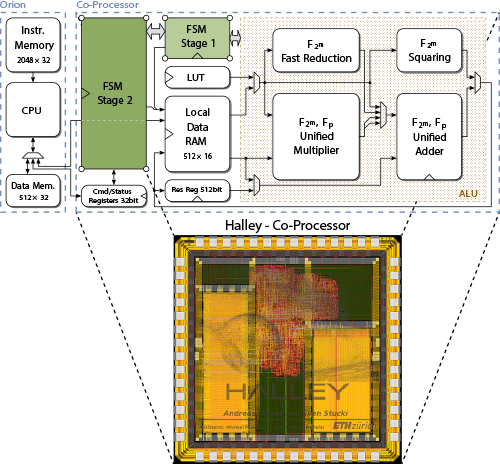
[[File:sem13h5-teaser.png|thumb|500px|Top: Simplified block diagram of the final hardware architecture attached to the Orion microprocessor (redesigned OpenRISC architecture). Bottom: Layout of the final chip called Halley.]] | [[File:sem13h5-teaser.png|thumb|500px|Top: Simplified block diagram of the final hardware architecture attached to the Orion microprocessor (redesigned OpenRISC architecture). Bottom: Layout of the final chip called Halley.]] | ||
| − | ==Short Description== | + | ===Short Description=== |
An application-specific instruction-set processor (ASIP) tailored to | An application-specific instruction-set processor (ASIP) tailored to | ||
verify digital signatures according to the Elliptic Curve Digital | verify digital signatures according to the Elliptic Curve Digital | ||
| Line 22: | Line 23: | ||
verification on a general purpose CPU. | verification on a general purpose CPU. | ||
| − | === | + | ===Project Information === |
| − | + | * Date: Fall Semester 2013 (sem13h5) | |
| − | + | * Students: Sven Stucki, Andreas Traber | |
| − | + | * Supervisors: [[:User:mbgh|Michael Muehlberghuber]], [[:User:Muheim|Beat Muheim]] | |
===Professor=== | ===Professor=== | ||
| − | + | * [http://www.dz.ee.ethz.ch/en/general-information/about/staff/uid/364.html Hubert Kaeslin] | |
===Links=== | ===Links=== | ||
| Line 35: | Line 36: | ||
| − | [[ | + | [[Category:Cryptography]] |
| + | [[Category:Semester Thesis]] | ||
[[Category:Digital]] | [[Category:Digital]] | ||
| + | [[Category:ASIC]] | ||
[[Category:Completed]] | [[Category:Completed]] | ||
| − | |||
[[Category:2013]] | [[Category:2013]] | ||
| + | [[Category:Muehlberghuber]] | ||
<!-- | <!-- | ||
Latest revision as of 12:26, 26 March 2015
Short Description
An application-specific instruction-set processor (ASIP) tailored to verify digital signatures according to the Elliptic Curve Digital Signature Algorithm (ECDSA) based on the NIST B-233 standard was developed. The resulting chip, called Halley, features a 16-bit wide unified datapath for both the binary and prime finite-field arithmetic, required to finish an ECDSA signature verification. It hosts a 2KB dual-port memory for data storage and a 6KB single-port instruction memory. A two-stage finite-state machine (FSM) controlling approach is used to realize the finite-field arithmetic. Moreover, the top-level controlling entity is made up by a programmable control unit, which realizes the elliptic-curve-specific operations. Halley finishes digital signature verification at its maximum frequency of 167Mhz within about 1.9Mcycles, meanwhile consuming an average power of 70mW.
In addition to the "pseudo-processor-controlled approach", the finite-field arithmetic supporting datapath was combined with an OpenRISC microprocessor, thereby enabling accelerated ECDSA verification on a general purpose CPU.
Project Information
- Date: Fall Semester 2013 (sem13h5)
- Students: Sven Stucki, Andreas Traber
- Supervisors: Michael Muehlberghuber, Beat Muheim